Nearly 20 years ago, I participated in the governmental debates about Huawei and whether or not the Chinese multinational should be allowed to purchase a telecommunications company that also contracted with the U.S. government. Much of the debate focused on whether there was a smoking gun that connected Huawei to espionage, technology transfers, or other malfeasance. For many, no smoking gun; no problem. We soon learned differently: Huawei inserted backdoors into the African Union headquarters and used another country’s lawful intercept capability to monitor targets of Beijing’s ire.
The United States, however, has continued to think about protective countermeasures in this same legal framework, even as technology permeates ever more deeply into our daily lives. Modern cars, not just electric vehicles, are mobile computers, equipped with sensors and to which people connect their smartphones. Smart home devices, from refrigerators and thermostats to televisions, gaming systems, and more, all connect to an Internet created with security as an afterthought. These devices offer new ways to monitor our activities; but they can also be hijacked by malicious actors, like China’s Ministry of State Security (MSS).

Imagine finding out that your television and thermostat were part of a denial of service attack or lending their compute to a brute force log-in. This is not a paranoid fantasy, but a reality that already has emerged. At the center of the global market for TVs are PRC corporations such as HiSense and TCL. They have been able to penetrate the American market through partnerships with tech firms such as Google, Amazon, and Roku. These companies provide the appearance of an American product, but the underlying tech layers, including the hardware and firmware, are still connected to the Chinese original equipment manufacturer.
Beijing’s expansive view of national security, which is defined by the absence of threats, is enshrined in its 2015 National Security Law. This law provides legal support to a sweeping intelligence effort that is always in search of enemies at home and abroad. Inside China, for instance, Beijing has monitored water and electricity usage to determine whether guests are visiting homes. Outside China, Americans should wonder whether they themselves could be targeted.
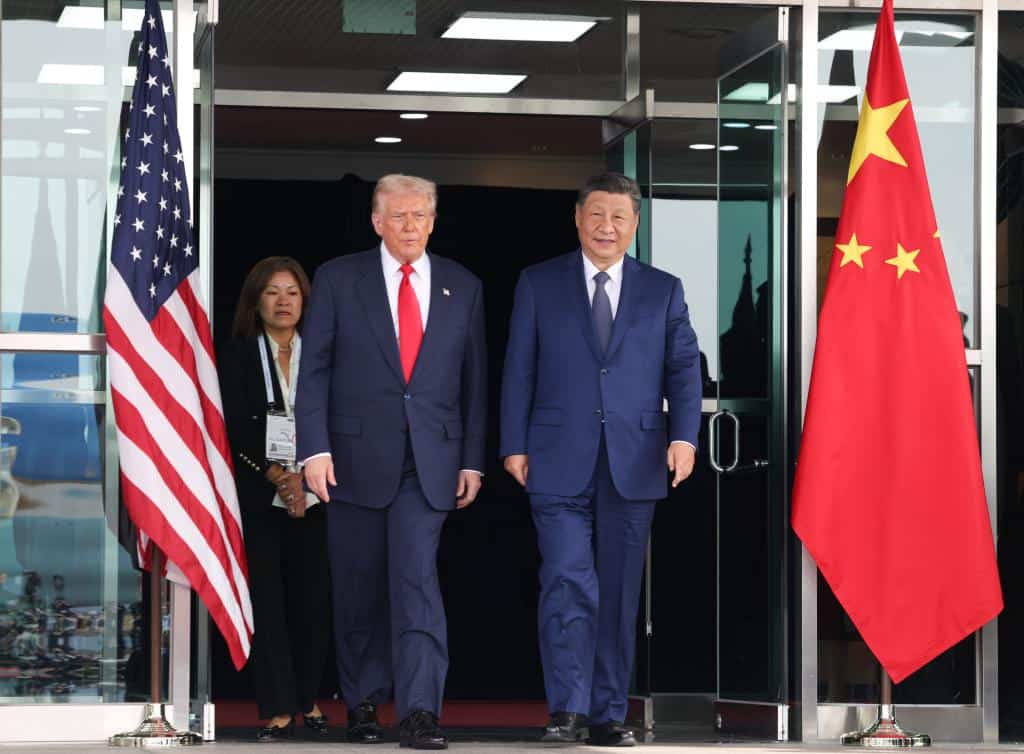
The Chinese Communist Party’s leaders have long held that there is a basic incompatibility of its system of governance and that of Western, liberal democratic capitalist ones. They believe that this incompatibility will eventually lead to conflict. Mao Zedong may be dead, but his ambition for the People’s Republic has persisted. When Xi Jinping began his terms in office in 2012, he set out to build a version of the world in the Chinese vision. In 2020, he introduced the concept of “the East is rising and the West is declining” and proclaimed that there are “great changes unseen in a century.” Xi believes that “American decline” presents numerous opportunities for China to surpass the United States in terms of national power. He has also said that China’s “struggle and contest with Western countries is irreconcilable, so it will inevitably be long, complicated, and sometimes even very sharp.”
The Party’s far-reaching ambitions have real-world implications for American consumers. Major companies in the People’s Republic of China are increasingly intertwined with the CCP, especially those in strategic sectors with global reach. All have party committees that shape corporate decision-making and strategy and play a role in personnel selection.
Through participation in bidding for state and military procurement contracts, embedded Party-aligned structures, and corporate leadership concurrently holding CCP positions; manufacturers like Xiaomi, TCL, and Skyworth maintain strong links with the PRC government.
For any Internet-of-Things devices, there are additional risks relating to personal privacy and national interest. Evidence that the PRC is capable of exploiting Chinese digital infrastructure overseas is mounting. In a recent petition filed by the Texas Attorney General, HiSense smart TVs have been accused of spying on users by taking screenshots every 500 milliseconds, tracking viewing habits and subsequently sending this user data to the PRC. A U.S. government agency found TCL smart TVs allowed unauthorized access to the devices’ data and media files. And users discovered Skyworth Group smart TVs were sending back data about other devices in users’ homes back to a Beijing-based company’s servers.
Data collection via these devices is extensive, and data residency claims are frequently contradicted or left ambiguous by the manufacturers’ own privacy policies and technical infrastructure. For instance, consumers are only vaguely informed that HiSense “may” export their data without an opt-out mechanism. This type of constant surveillance aims to create detailed household-level profiles, giving the Chinese state access to the private lives of millions of Americans to be used for any purpose.
But most consequential is the ability of Chinese manufacturers to modify device behavior at scale through over-the-air firmware updates. These allow for privileged access to engineering teams operating under PRC jurisdiction—and potentially acting at the government’s behest.
The most obvious counterarguments to these concerns are, first, everyone, including Western companies, is spying through these devices all the time, and, second, that Chinese companies would lose commercially if they were ever caught acting inappropriately or nefariously.
The first argument assumes that there is no distinction between private companies and governments. Google or Siemens might collect information about user behavior; however, these companies are distinct and separate from the state’s police and intelligence powers. If the state is able to exploit their information collection, it does require a legal process to breach the private-public divide. As noted above, that divide is not meaningful with respect to Chinese companies or where the locus of control is inside China.
The second argument is false empirically. Chinese companies have been caught doing nefarious things without suffering meaningful consequences. Huawei being caught in Africa did not slow its advance in global 5G infrastructure. Moreover, once the data is exfiltrated, it becomes incredibly difficult—short of national-level intelligence collection capabilities—to detect how that data is being used or misused.
At this point, there is little to argue for continuing inaction.
Action taken by individual U.S. states is encouraging and often happens more rapidly than federal action, the piecemeal nature of these enforcement measures results in a fragmented regulatory landscape.
First, the United States needs to change its legalistic mindset about corporate actors connected to an adversary. The risks here are high. The consequences are widespread. Prudence as a principle is warranted. To return to the smoking gun analogy, there is copious evidence of repeated stolen information, intimidation of U.S. citizens and residents, and U.S. companies forced into bankruptcy after falling victim to technology theft and predatory PRC policy. If anything, there is too much smoke for people to see clearly how serious the risks are.
U.S. courts have recognized that the corporate and party-state structures mean that Chinese firms can be seen as part of an integrated whole. State ownership, shared resources (including people), inadequate capital for subsidiaries, and a lack of barriers between subsidiaries and parent companies create potential vulnerabilities to legal action. Even companies with a mixed ownership structure, like HiSense, which has a large stake from the Qingdao State-owned Assets Supervision and Administration Commission (SASAC) holding company, might be treated as arms of the party-state, enabling legal actions that stem from Beijing’s stated ambitions and policies.
Second, policymakers should set security standards for all devices that will plug into the Internet-of-Things ecosystem. A challenge to the entire ecosystem requires a systemic response to protect the fragility created by connectivity. Such standards would be country-agnostic and simply demand built-in protections for American consumers.

If we want to avoid country of origin and related transshipment problems, then security standards, local governance, and allowable routine business activities will need to dictate what kind of devices with what kind of sensors and connectivity are allowed entry into the United States. The rule has to be watertight. Beijing long ago denied routine due diligence activities and site inspections where it had any sensitivity, so inspection-based regimes are not viable. To deal with original equipment manufacturers and transshipment issues, supply chain tracking and clear penalties for violators need to be part of the solution. Rather than being “anti-China,” this kind of rule could offer leverage for normal business practices to be routine in U.S.-China interactions.
Third, a wide range of specific authorities exist to regulate or even ban problematic hardware and software in the information and communications technology services (ICTS). These ICTS authorities under the U.S. Department of Commerce—which have bipartisan backing and have been sharpened by both Democrats and Republicans—should be considered applicable for Internet-of-Things devices. The Federal Communications Commission also has rulemaking authorities that might be applied as well to address the threats that specific companies pose to Americans.

Peter Mattis is President of The Jamestown Foundation and a former CIA counterintelligence analyst.