On July 7, Microsoft was preparing to release a patch for a critical vulnerability in its SharePoint software, used by more than 200 million users worldwide. But Chinese hackers got there first.
The hackers staged a massive global campaign one day before Microsoft had planned to distribute its fix, hitting hospitals, national labs and U.S. government agencies, including the National Nuclear Security Administration, responsible for maintaining America’s nuclear arsenal.
Now, Microsoft is investigating whether an early tip-off by the company itself may have triggered the hack, according to reporting by Bloomberg. The software giant’s attention has focused on a 17-year old program through which Microsoft regularly provides around 100 trusted cybersecurity partners early information about pending security patches. At least 19 Chinese companies are part of this Microsoft Active Protections Program (MAPP), a review by The Wire has found.
Experts say that their inclusion is alarming, given the blurred lines between cybersecurity firms, state security agencies and offensive hacking groups in China. Among the Chinese MAPP partners is a company founded by members of China’s first hacking group, and another that has hired large numbers of so-called ‘patriotic’ hackers. Given the timing of the hack, the suspicion is that one or more companies may have shared information with hacking groups or the Chinese government, enabling the hack.
Microsoft, though, is in a difficult position. If the Redmond, Washington-based company wants to keep doing business in China, it’s hard to avoid including Chinese partners in programs like MAPP — even at a time when Chinese companies are increasingly required to support Beijing’s priorities.
“It comes down to Microsoft trying to balance protecting users in China with the possibility that this information could be used in offensive attacks,” says Dakota Cary, a China-focused consultant at SentinelOne, an American cybersecurity firm. “Microsoft should be able to protect its customers. These companies are abusing this trusted process for distributing information.”
The race to fix the vulnerability in SharePoint began in mid-May, when a Vietnamese researcher demonstrated a weakness in the document management software at a hacking competition in Berlin. Western software companies often stage such ‘bug bounty’ competitions to help find security flaws in their products. Microsoft scrambled to deploy a fix, which was scheduled for release on July 8.
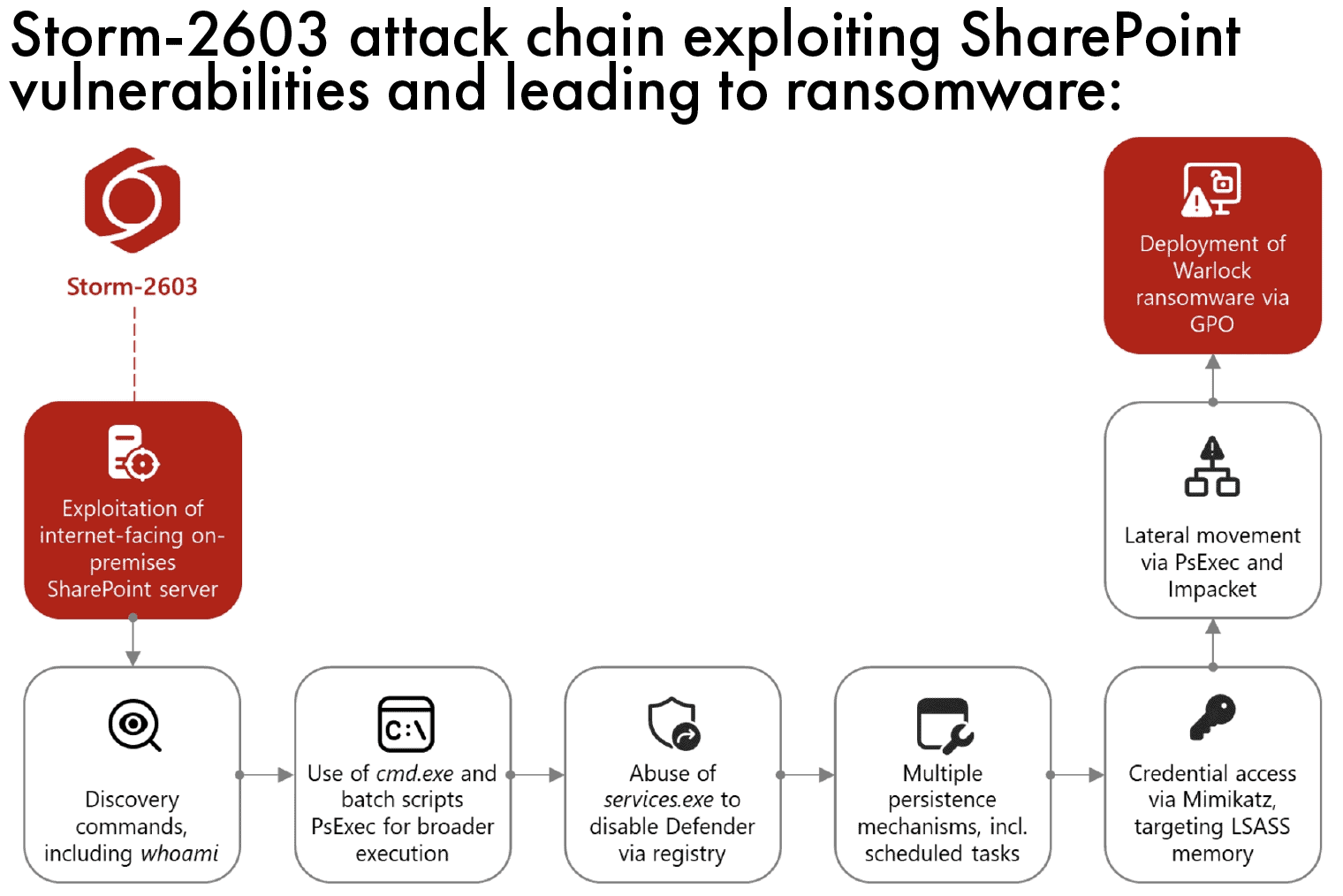
But the day before, at least three Chinese hacking groups exploited the vulnerability to breach businesses, governments and other organizations and steal sensitive information. They include two “nation-state actors” Microsoft has identified as Linen Typhoon and Violet Typhoon, both of which have historically focused on intellectual property theft and espionage. Another suspected Chinese-based actor labelled Storm-2603 exploited the software flaw to deploy ransomware, Microsoft says.
Cybersecurity experts say the timing of the hack and the simultaneous attacks by multiple hacking groups are both highly unusual — and telltale signs the Chinese hackers benefited from a leak, potentially via one or more of the Chinese members of the MAPP program.
It comes down to Microsoft trying to balance protecting users in China with the possibility that this information could be used in offensive attacks. Microsoft should be able to protect its customers.
Dakota Cary, a China-focused consultant at American cybersecurity firm SentinelOne
“Having Chinese partners in the MAPP program is still a good thing because it gives [the U.S.] a lot more visibility into what China is able to do,” says Adam Kozy, founder of SinaCyber, a China-focused cybersecurity consultancy. “But this isn’t the first time that Chinese APTs [advanced persistent threat actors] have gotten hold of a vulnerability that hasn’t quite been patched yet [by Microsoft]. And it seems like there hasn’t been much oversight or investigation into which partners are behaving responsibly.”
Microsoft established MAPP in 2008 to give trusted security vendors a headstart in preparing defensive measures for their customers. The company notifies most partners of impending patches 24 hours in advance; a smaller subset of vetted companies can get information as early as two weeks ahead of time.
While China accounts for less than two percent of Microsoft’s global revenue, Chinese companies account for an outsized share of its MAPP partners — roughly one-sixth. They include companies such as NSFOCUS, a cybersecurity company founded by members of the Green Army, China’s original patriotic hacking group, and VenusTech, a prolific hirer of former patriotic hackers. Other partners include more established tech giants like Alibaba, Baidu and Tencent.

“We continually evaluate the efficacy and security of all of our partner programs and make the necessary improvements as needed,” a Microsoft spokesperson said in a statement. “Our partner ecosystem is an important piece of our security response and helps ensure customers have early protections regardless of the AV [antivirus] products they chose.”
NSFOCUS and VenusTech did not respond to requests for comment.
Cybersecurity companies — Chinese or otherwise — often hire former hackers, whose talents and experience can be valuable assets. Many of China’s top cybersecurity firms were founded by, or have hired, former ‘patriotic’ or ‘red’ hackers, who came of age in the 1990s and whose intrusions were often driven by nationalism and personal ambition. In the years since, they have professionalized and commercialized their operations.
“VenusTech and NSFOCUS are some of the oldest information security companies in China with large global businesses,” says Mei Danowski, a researcher and author of Natto Thoughts, a newsletter covering China’s cybersecurity ecosystem. “If they’re not on a sanctions list, I think it’s reasonable for Microsoft to choose them.”
Where Chinese cybersecurity companies differ, experts say, is in their willingness to go beyond providing clients with ways to defend their systems against hacking, to getting involved with “offensive” hacking operations. Take Qi An Xin Technology Group, a MAPP partner and one of China’s premier cybersecurity firms: as The Wire reported last year, with a 13 percent stake, it is the second largest shareholder in i-Soon Technology, a prolific Chinese hacking group whose own internal data was leaked last year.
Chinese cybersecurity firms are also under legal pressure to share early information they receive about software vulnerabilities — such as the one that affected Microsoft’s SharePoint — with the Chinese government. In 2021, China’s Cyberspace Administration, Ministry of Public Security and Ministry of Industry and Information Technology issued a joint regulation requiring industry actors to report all code flaws to the MIIT within 48 hours of their discovery.
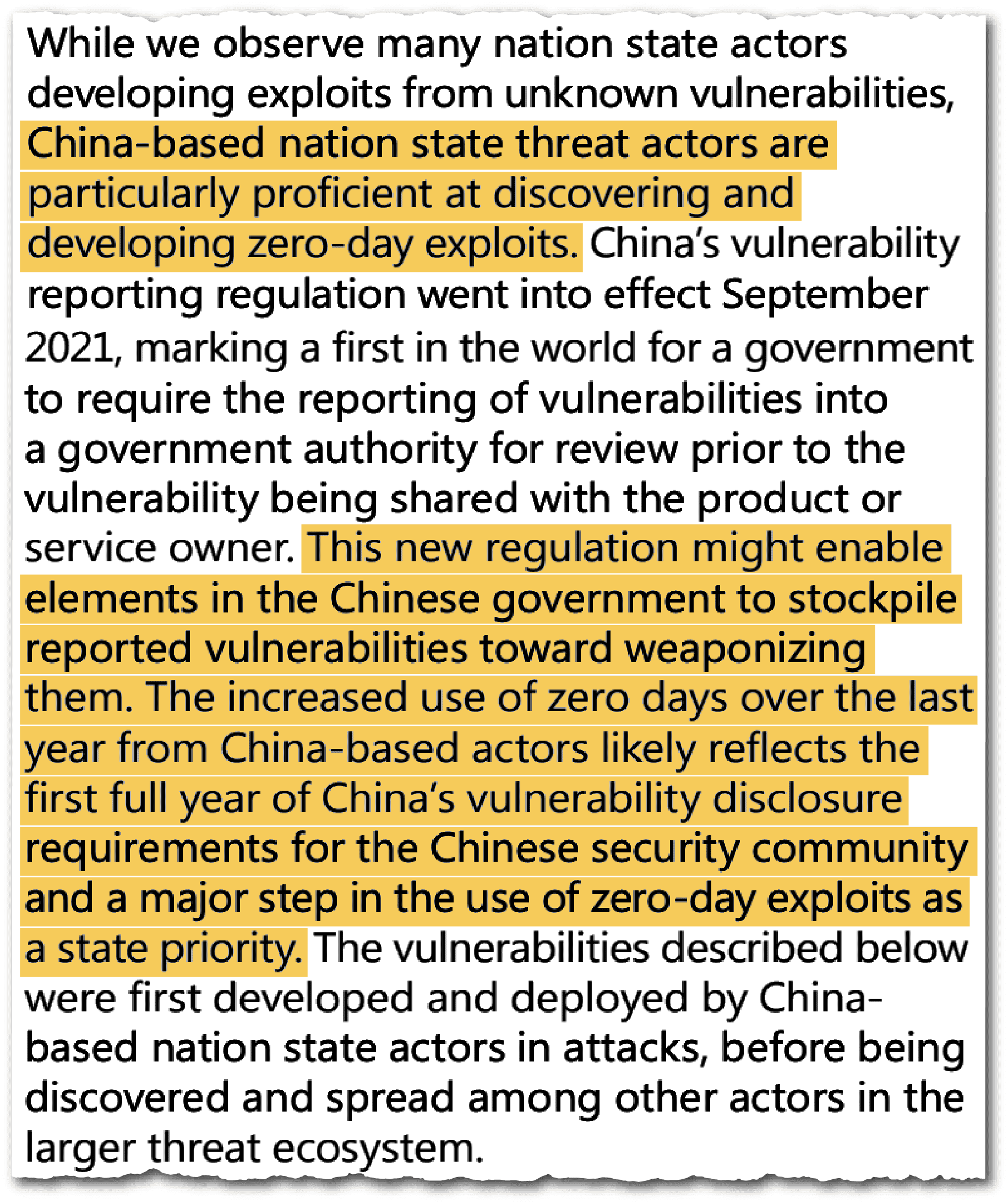
That regulation was nominally designed to strengthen China’s cybersecurity defenses. But evidence suggests that the Chinese authorities may be passing the information cybersecurity firms are providing on to hackers. According to research by Cary, the cybersecurity consultant, the Ministry of State Security (MSS) — China’s foreign intelligence service — can access any information about vulnerabilities that firms report.
Microsoft’s own 2022 Digital Defense report noted an increased exploitation of “zero day” vulnerabilities by Chinese actors immediately after the disclosure requirement coming into effect. Such vulnerabilities are software flaws unknown to their developers and for which there is no defense, making them the most serious type of security flaw.
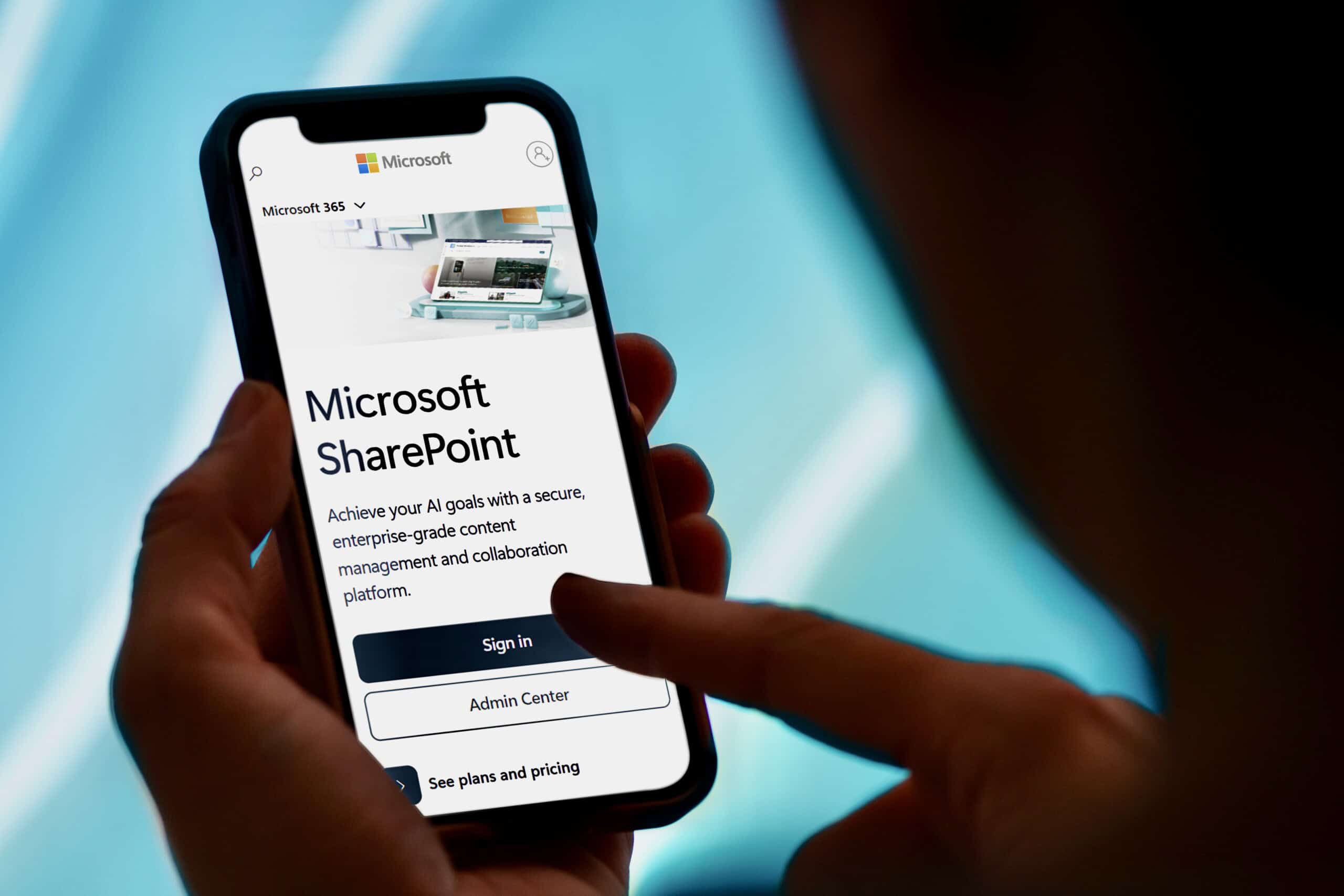
Experts say there could be another route through which the Chinese authorities are obtaining and then disseminating sensitive information to hackers. 12 out of 19 companies in Microsoft’s MAPP program are publicly listed as “technical support units” to the China National Vulnerability Database (CNNVD) which is run by the MSS. Ten of them are ‘Tier 1’ units, meaning that they submit at least 20 software vulnerabilities to the database every year, including at least three classified as “critical risk.”
Microsoft’s Chinese MAPP Partners
Microsoft has 19 Chinese companies listed among its trusted cybersecurity partners. 12 of those companies also have agreements with China’s Ministry of State Security to disclose critical software vulnerabilities.
| Participant Name | Headquarters | MSS Vulnerability Database Technical Support Unit | Description |
|---|---|---|---|
| Alibaba (China) Co. | Hangzhou | ||
| Antiy Labs | Beijing | Tier 1 | |
| Asiainfo Security Technologies Co. | Nanjing | Tier 1 | |
| Baidu International Technology | Beijing | ||
| Beijing Huorong Network Technology | Beijing | ||
| Beijing CyberKunlun Technology Co. | Beijing | Tier 1 | |
| Beijing Rising Network Security Technology Co. | Beijing | ||
| Beijing Shengxin Network Technology Co. | Beijing | ||
| Beijing ThreatBook Security | Beijing | Tier 2 | |
| DBAPPSecurity Co. | Hangzhou | Tier 1 | |
| Fortcloud (Xiamen) Security Info Tech Co., Ltd. | Xiamen | ||
| Hansi Anxin (Beijing) Software Technology Co. (Hansight) | Beijing | ||
| H3C Technologies | Hangzhou | Tier 1 | Originally a joint venture between Huawei and 3Com. Now a joint venture between Tsinghua Unigroup and Hewlett Packard Enterprise. |
| Hillstone Networks | Suzhou | Tier 3 | |
| Legendsec Technology Co. Ltd | Beijing | Tier 1 | Subsidiary of Qi An Xin, one of China’s premier enterprise cybersecurity companies, which has also invested in i-Soon Technologies, a hacking group. |
| NSFOCUS | Beijing | Tier 1 | The “commercial branch” of China’s Green Army, founded by several former ‘red’ hackers. |
| Sundray Technology Co. Ltd | Shenzhen | Tier 1 | Subsidiary of Sangfor, a cybersecurity company that was previously a MAPP partner. |
| Tencent | Shenzhen | Tier 1 | |
| Venustech | Beijing | Tier 1 | One of China’s oldest cybersecurity companies. Known for hiring a large number of former patriotic hackers. Now under the control of China Mobile. |
A 2017 analysis by Recorded Future, an American cybersecurity company, found that the MSS likely passed high criticality vulnerabilities to its hacking teams and delayed their public disclosure. More recently, leaked chat logs from i-Soon, the hacking group, showed company executives discussing whether they could obtain details of a vulnerability from the Ministry of Public Security, further evidence of the government’s role as an information distributor.
This is information that was shared in good faith… [China] need[s] to feel some consequences for betraying that trust.
Adam Kozy, founder of SinaCyber, a China-focused cybersecurity consultancy
Microsoft has scrutinized members of the MAPP program for leaks before. In 2012, Microsoft kicked a Chinese company, Hangzhou DPTech Technologies Co., out of the program for disclosing information about a major vulnerability in its Windows operating system.
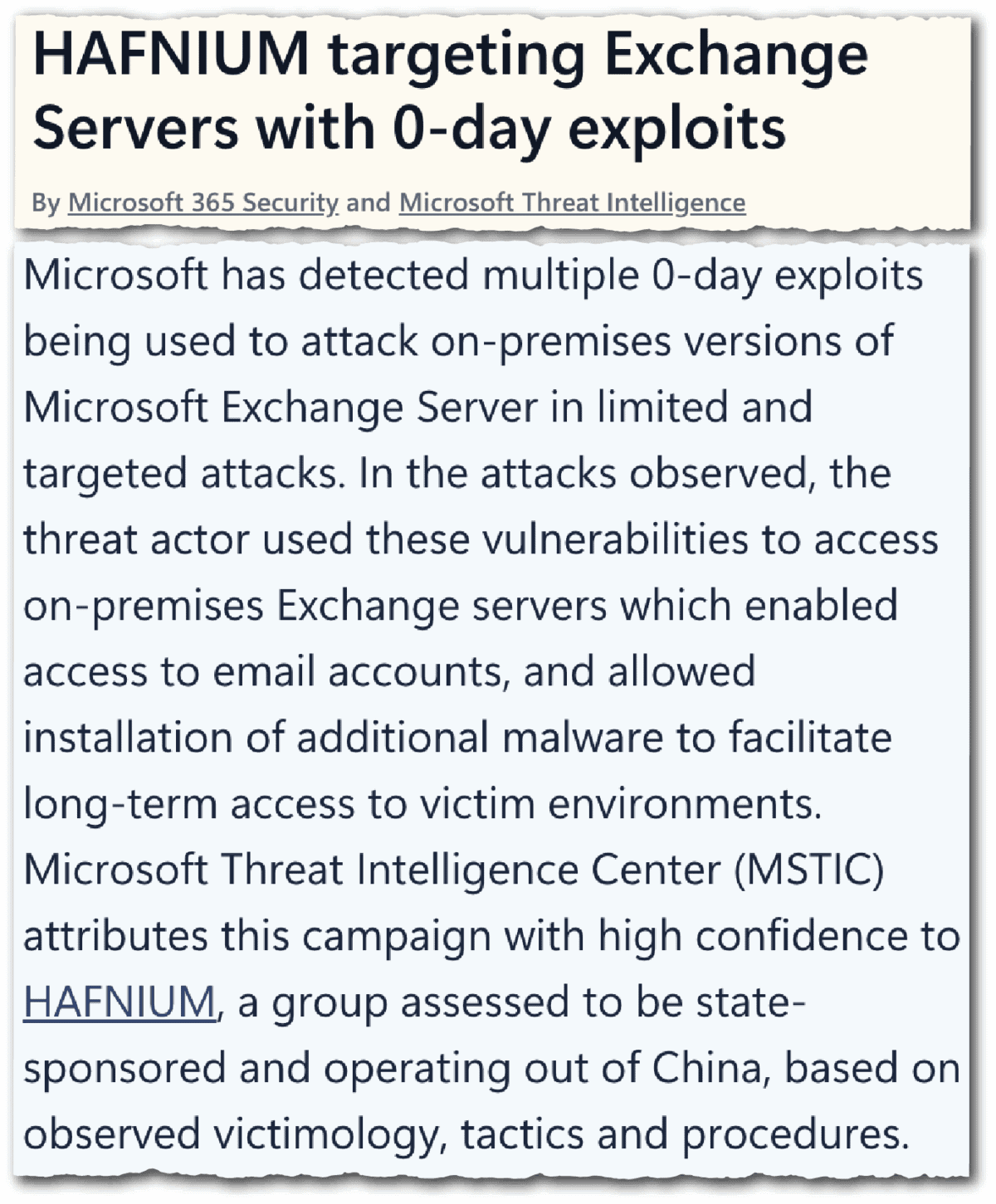
In 2021, Microsoft also scrutinized two unnamed Chinese MAPP partners, according to reporting by Bloomberg, for suspected leaking, after a Chinese group called Hafnium and other state-affiliated groups perpetrated one of the worst security breaches in the company’s history. Chinese companies have also been removed from MAPP after being hit with U.S. export controls, including Huawei and Qihoo360 in 2019 and 2020, respectively.
Experts say there are ultimately limits to what Microsoft can do to penalize leakers on its own. Any lasting fix would likely require intervention from Washington, whether via diplomatic measures or tougher penalties.
“This is information that was shared in good faith,” says SinaCyber’s Kozy. “They [China] need to feel some consequences for betraying that trust. How to do that is the trickier question, but I haven’t really seen any time where China has feared U.S. reprisal on this front. Absent that, this is going to continue to happen.”
Eliot Chen is a Toronto-based staff writer at The Wire. Previously, he was a researcher at the Center for Strategic and International Studies’ Human Rights Initiative and MacroPolo. @eliotcxchen