For years, western cybersecurity researchers have been tracking a sophisticated Chinese hacker group as it wormed its way into the systems of governments, universities and social media platforms. They labeled it with different aliases, including Fishmonger, Red Scylla and RedHotel.
By the end of last year, several teams had independently closed in on a likely company name: i-Soon Information Technology Co.

So when a data leak from i-Soon appeared online last week, it provided an unprecedented window for researchers to corroborate many of their suspicions about one of the most prolific actors in China’s hacker-for-hire industry. The leaks also revealed something surprising: the extent to which China’s hackers — between plundering foreign governments for sensitive information and surveilling ethnic minorities abroad on Beijing’s behalf — do business at home just like any ordinary company.
From contractual disputes with rivals, to staff arranging team-building events and griping about low pay, the leaked data dispel some of the mystique that has long surrounded China’s hackers. Public records further illustrate the shadowy company’s links to the legitimate side of China’s internet security industry, with its investors including one of China’s largest cybersecurity providers and a venture capital fund controlled by the Chinese Academy of Sciences, the state-backed national science and technology research institute.
“It’s important for people to understand that all these companies are ultimately businesses with profit as their bottom lines,” says Mei Danowski, a cyber threat researcher and expert on China’s cybersecurity ecosystem. “They work together to get contracts… and build their reputations by cooperating with institutions, because they know that’s what’s required for them to do business.”
The leaked documents show that i-Soon sought to extract data from government agencies in at least 20 countries and territories, including Hong Kong, Taiwan, India, South Korea, Thailand, Malaysia and the U.K. The company’s hacking tools were used to conduct email phishing campaigns, unmask users on X (formerly Twitter) and take over their accounts. One spreadsheet showed that the company had hundreds of gigabytes of road-mapping data from Taiwan, which could aid China’s military in planning an invasion. In a September 2022 presentation that preceded the leaks, Kris McConkey, a lead researcher at PwC’s global cyber threat intelligence practice, described i-Soon as a “significant superpower” and “one of the most prolific, deeply connected, and technically advanced actors.”
Meanwhile, at home, well-connected investors and partners helped Chengdu-based i-Soon grow and secure new clients. Its founder and largest shareholder is Wu Haibo, a well known Chinese hacker and one-time member of the “Green Army,” one of China’s oldest “patriotic” hacktivist groups. Starting in the late 1990s, groups like the Green Army leveraged their technical skills to vandalize or disrupt access to official websites in the U.S., Japan and Taiwan.
As China’s internet matured in the early 2000s and Beijing began discouraging the Green Army’s activities, hacktivists like Wu “were the first ones to start [cybersecurity] companies,” says Danowski. “They saw an opportunity. If they had a company, they could do training, develop software and work for the government.”
…all these companies are ultimately businesses with profit as their bottom lines. They work together to get contracts… and build their reputations by cooperating with institutions…
Mei Danowski, a cyber threat researcher and expert on China’s cybersecurity ecosystem
I-Soon has received significant backing from external investors, too. Company ownership records from WireScreen show that i-Soon took on investment from a fund controlled by Cash Capital, the venture capital arm of the Chinese Academy of Sciences in 2018. That fund holds a 3.1 percent stake in i-Soon.
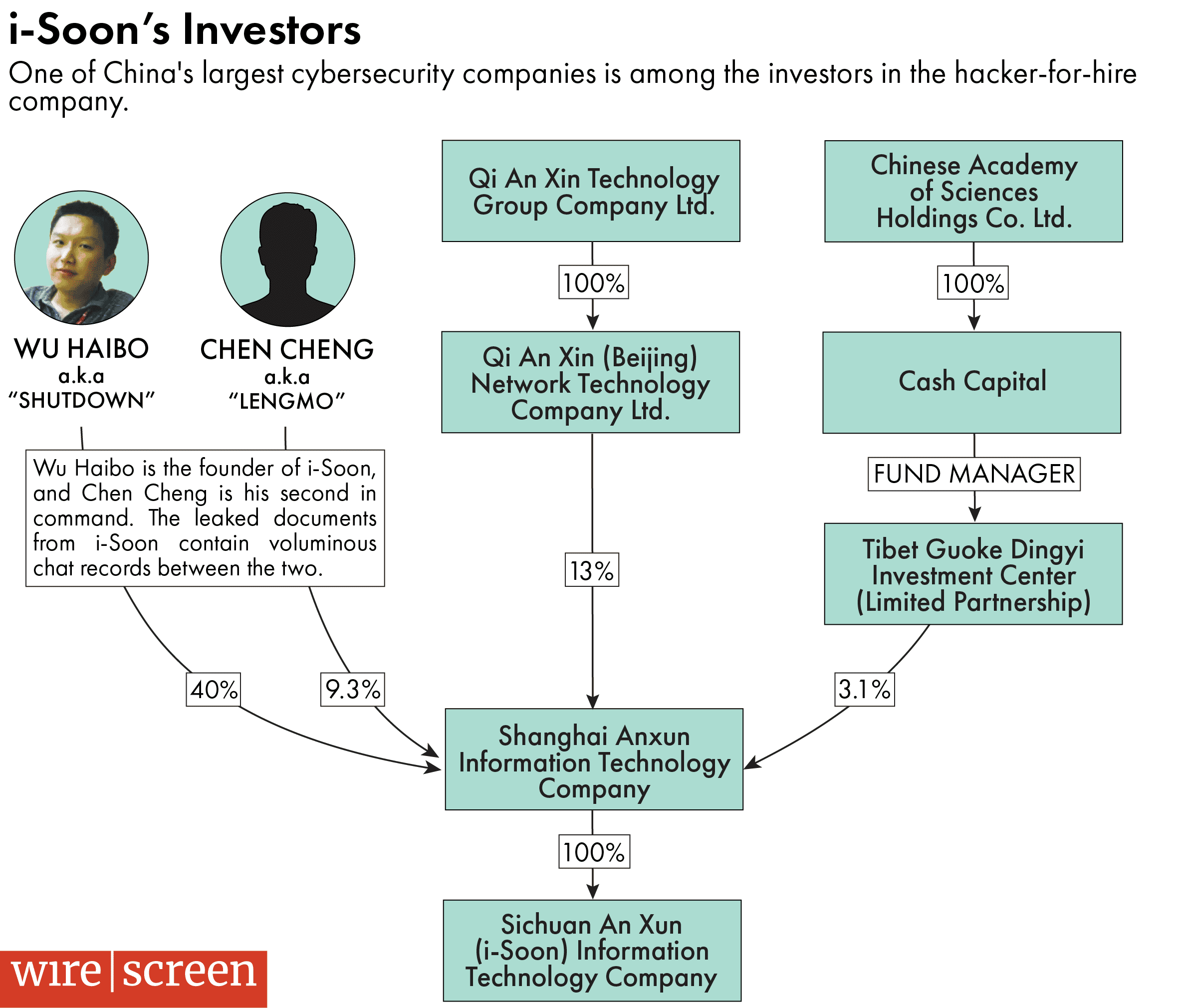
Also in 2018, i-Soon received a significantly larger investment from a wholly-owned subsidiary of QiAnXin Technology Group, a leading Chinese cybersecurity firm that sells protection to companies and the Chinese government. QiAnXin, a publicly listed company that was spun out from Qihoo360, China’s largest consumer internet security provider, in 2019, is currently i-Soon’s second largest investor, with a 13 percent stake. The company was a sponsor and service provider for the 2022 Beijing Winter Olympics.
Kris McConkey presents on Shanghai Anxun Information Technology during LABSCon, September 2022.Credit: SentinelOne via YouTube
In most countries it would be unusual for a cybersecurity firm in the business of protecting clients to be simultaneously invested in a company engaged in illegal hacking, says Dakota Cary, a China-focused threat researcher with SentinelOne, an American cybersecurity company.
“Western cybersecurity firms do offensive hacking against their clients to improve their security, so it’s not outlandish to see offensive and defensive capabilities end up in the same place,” he says. “But to see [a cybersecurity firm] doing operations on behalf of the state is quite unique.”
Companies like i-Soon and QiAnXin might be motivated to partner up for both business and strategic reasons. Edward Tsai, a former QiAnXin executive, explained the company’s motivation for investing in smaller cybersecurity firms in a 2021 interview with the Tech Buzz China podcast: “We started our own cybersecurity fund… that invested in a number of cybersecurity companies to help as a pipeline for QiAnXin for understanding the market, for acquisitions and whatnot.”
…it’s not outlandish to see offensive and defensive capabilities end up in the same place… But to see [a cybersecurity firm] doing operations on behalf of the state is quite unique.
Dakota Cary, a China-focused threat researcher with SentinelOne, an American cybersecurity company
For i-Soon, receiving investment from a more established player could unlock training opportunities, as well as additional work . The documents suggest that i-Soon occasionally served as a subcontractor on government contracts procured by QiAnXin.
“In China… people like to buy from larger companies in general,” explained Tsai on the Tech Buzz China podcast. “So sometimes the startups will work together with larger companies like QiAnXin… to sell together. Like the old adage people say: ‘you don’t get in trouble for buying from IBM.’”
But the close relationship with QiAnXin also frustrated executives at i-Soon at times. Chat logs show executives lamenting that several skilled engineers were poached by QiAnXin and i-Soon employees discussing their chances of getting a job there.
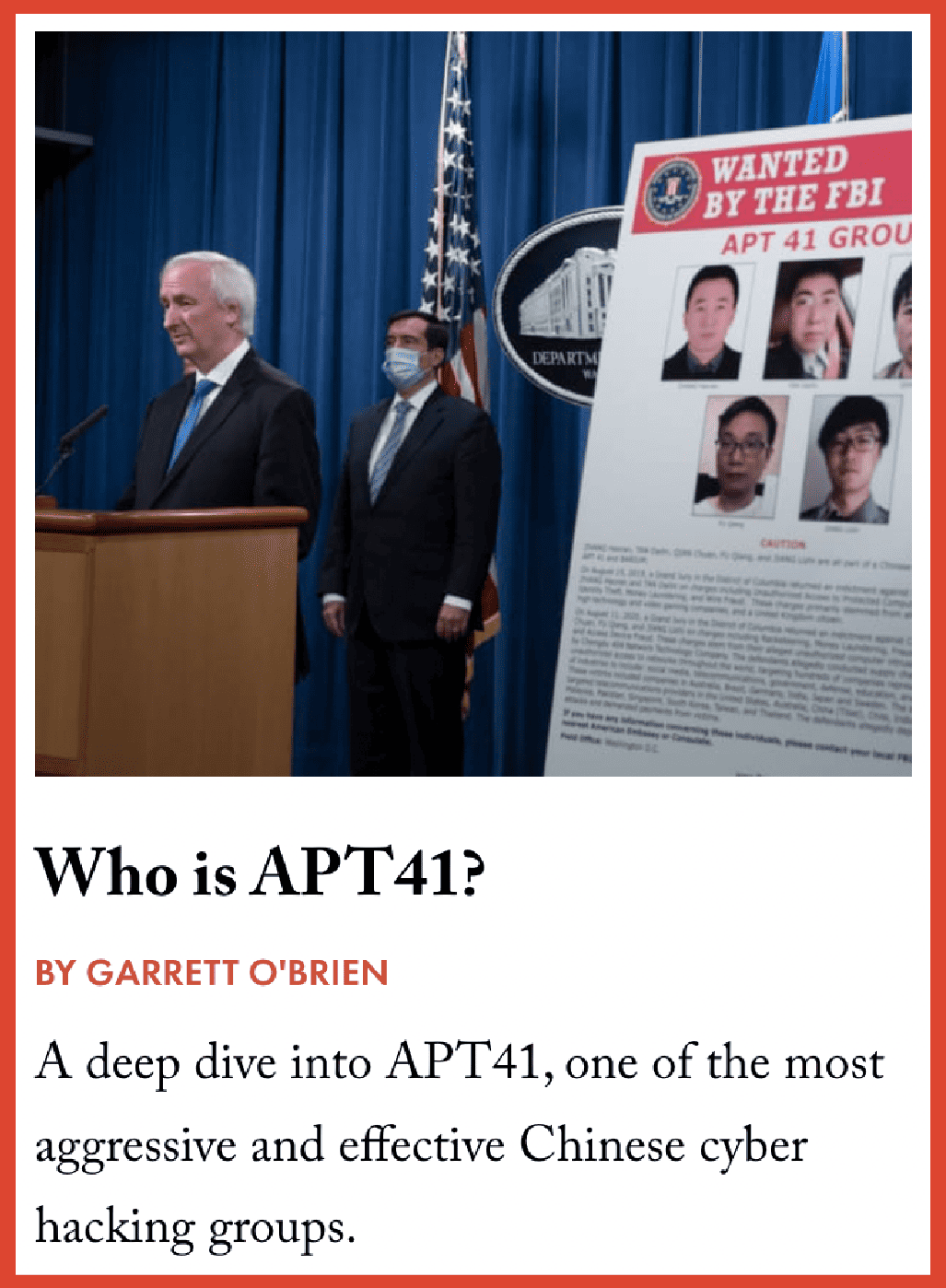
The documents also reveal the tumultuous relationship that i-Soon had with another partner: Chengdu 404 Network Technology Co., the company allegedly behind another prominent Chinese hacking group APT41. In 2020, three alleged members of APT41 were indicted by the Justice Department. Documents show that the two companies were business partners as well as competitors, supplying each other with technical services and cooperating on research. On occasion, the two companies would conspire to manipulate government contract bidding processes.
For western cybersecurity researchers, the documents confirmed what they had long suspected about the interplay between China’s hacking groups, which can make it hard to distinguish their activities. “Chinese firms share a lot of tools, code and network infrastructure,” says Mathieu Tartare, a senior malware researcher at ESET, a cybersecurity firm. Hacker groups that observers have assumed were one entity could actually be a multitude of Chinese companies wheeling and dealing with one another, illustrating the challenge foreign threat researchers face with penetrating and keeping track of China’s hacking industry.
For example, researchers like Tartare had long tracked APT41’s activities under the alias Winnti Group, but he says “around 2019, we realized Winnti Group was an umbrella. It didn’t mean anything, as there are a lot of different actors using the same malware.”
The leaked messages also show that i-Soon and Chengdu 404 had a falling out starting in 2022, stemming from i-Soon’s failure to make payments it owed Chengdu 404 of more than RMB 1 million ($140,000). Last year, Chengdu 404 sued i-Soon in court, in a dispute over a software development contract.
That, researchers speculate, may provide clues to the origins of this unprecedented leak. Uploading the data to Microsoft’s GitHub suggests that the leaker was targeting foreign audiences. What is clear, they say, is that the leaked documents seemed designed to embarrass i-Soon and damage its business.
A note left by the leaker on GitHub alongside i-Soon’s data read: “i-Soon’s information is unreliable. It scams government agencies.”
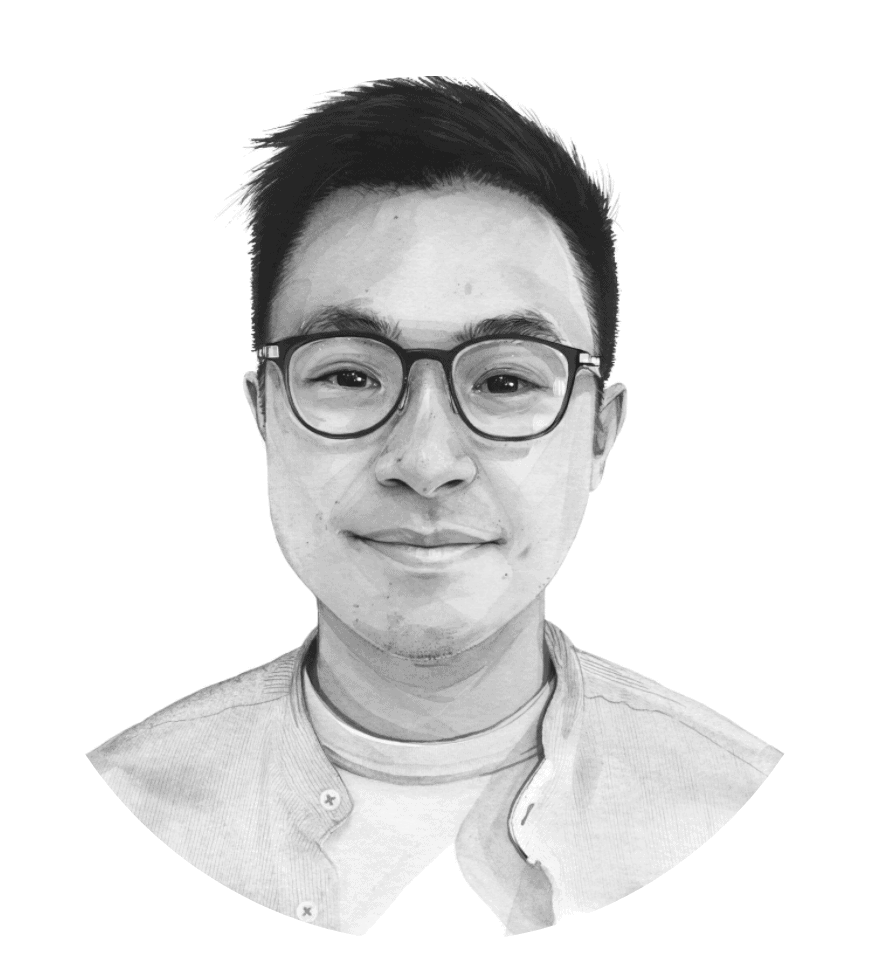
Eliot Chen is a Toronto-based staff writer at The Wire. Previously, he was a researcher at the Center for Strategic and International Studies’ Human Rights Initiative and MacroPolo. @eliotcxchen