It began with a Toyota RAV4, idling on a quiet street in Manila. The air was humid, and the city buzzed with activity. Inside were three men. One, Deng Yuanqing, was a Chinese national and the others were Filipino, posing as surveyors. On the dashboard: a mounted tablet, connected to a Global Navigation Satellite System. In the back seat: a high-powered imaging drone and a custom-built data relay antenna. They weren’t lost, nor were they tourists. They were closely observing a sensitive U.S. military base. And they were mapping it in meticulous detail.
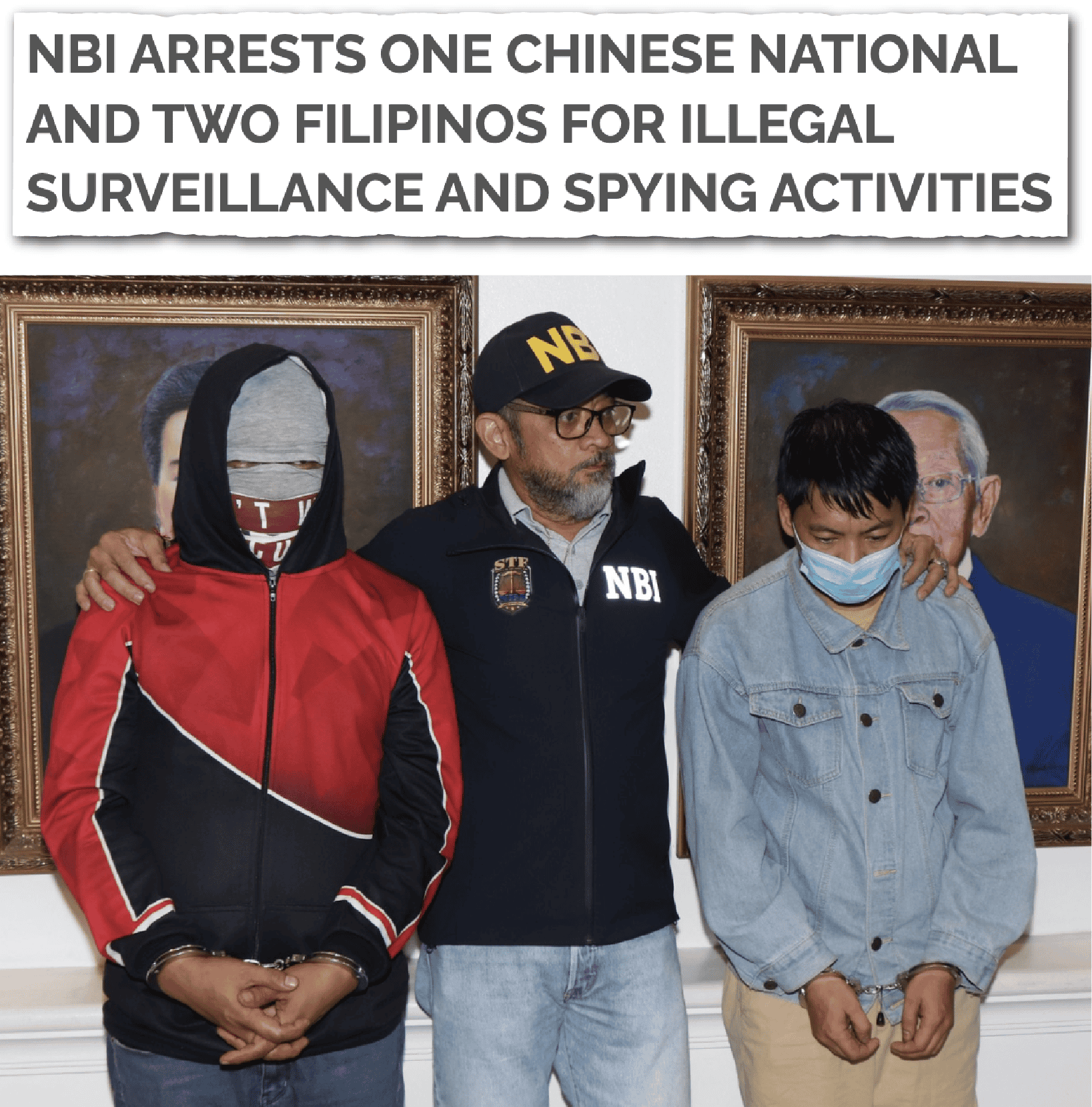
On January 17, 2025, Philippine security forces moved in. Deng and his team were arrested in Makati, the country’s financial district. Days later, five more Chinese nationals, claiming to be Taiwanese tourists, were detained on the island of Palawan, just miles from key Philippine naval outposts and U.S. rotational facilities. Each arrest unraveled another layer of a chilling reality: China wasn’t interested in using its agents to map the region just for the sake of it. Rather the targets of the motley surveillance crews were airstrips, fuel depots, radar towers, and ammunition storage sites, everything that would need to be hit first in the event of war between China and the United States.
Those operations in the Philippines were pieces of a global mosaic of espionage, part of a larger intelligence architecture designed to make one of the most dangerous weapons on Earth — China’s hypersonic missile force — even deadlier and more accurate.
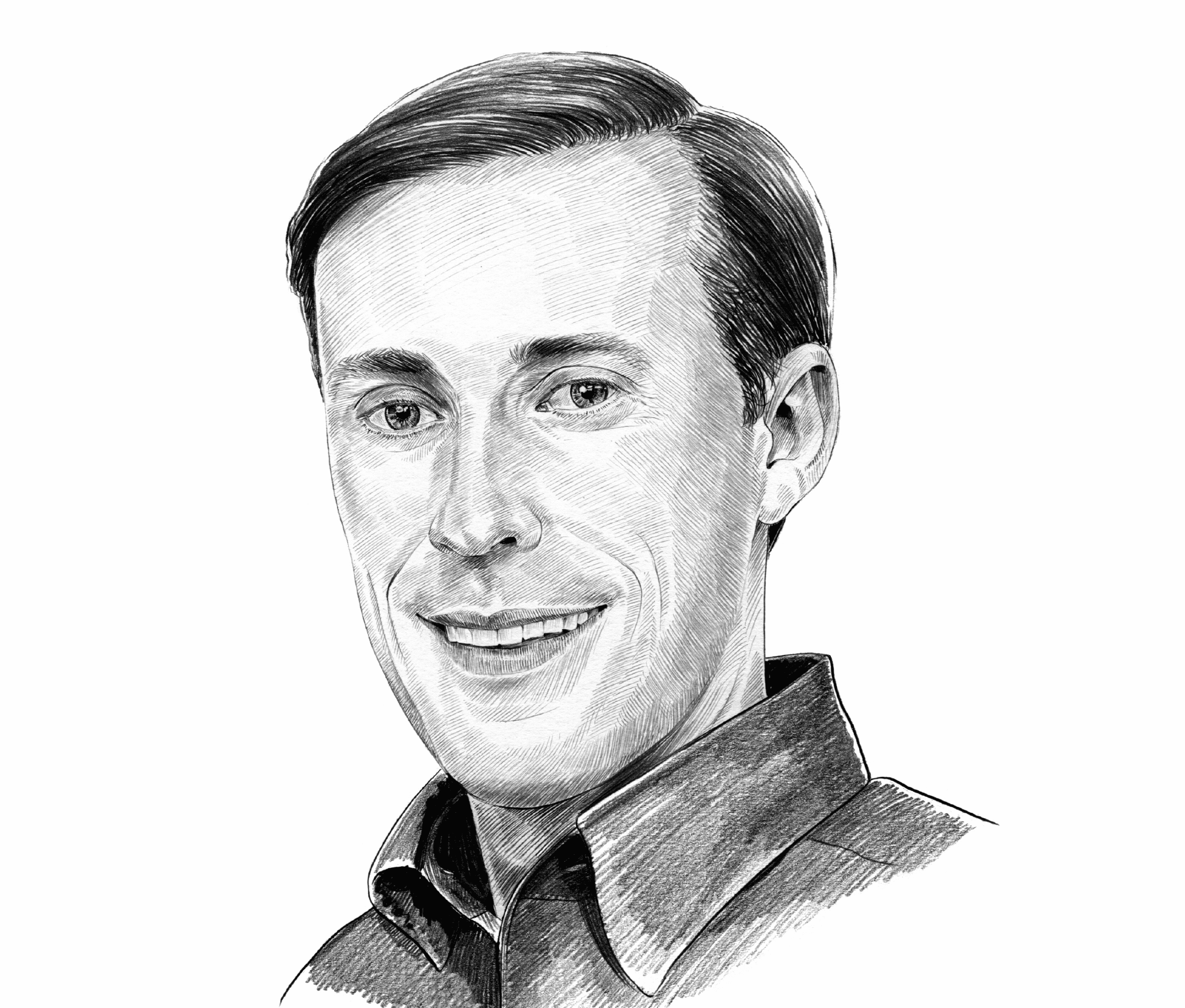
With speeds exceeding Mach 5, maneuverability that defeats conventional missile defense systems, and precision guidance that depends on exact geolocation data, hypersonic weapons are not designed for forewarnings. They’re designed for preemption and lethality. And the most vulnerable targets are the forward bases that provide the U.S. military its reach across the Pacific: Guam, Okinawa, Palawan, Subic Bay. The hypersonic missile force relies on having every hangar mapped, every fuel depot logged, every flight line measured — data fed into fire control systems thousands of miles away.

The People’s Liberation Army Rocket Force (PLARF) doesn’t need to land troops on U.S. soil to cripple this country’s defenses in the event of war; it only needs to hit hard, first, and with precision. Such a strike, Chinese military planners no doubt consider, could be enough to deter America from coming to Taiwan’s assistance in a PRC–Taiwan-armed conflict. The idea would be to strike with “shock and awe” and break, from the very outset, the American will for any such war by giving them a heavy taste of the costs they would have to bear. At hypersonic speeds, any such first strike on U.S. bases could be over before the first alert reaches a command post or triggers air defense systems. For decades, the United States bet on distance as a form of defense in depth — on deep supply lines, secure bases, and technological overmatch. But hypersonic weapons make distance significantly less relevant. Geography no longer protects us. And in a world in which minutes separate detection from destruction, there is no room for error.
The spy ring in the Philippines wasn’t gathering intelligence for trivial matters. It was drawing a kill list, a system of first-strike capability, powered by espionage, precision technology, and the ruthless logic of deterrence through dominance.
When Air Force Secretary Frank Kendall III delivered his address at the Air & Space Forces Association’s Air, Space & Cyber Conference in September 2021, he had been in office only two months. A graduate of West Point with a master’s degree in aerospace engineering from the California Institute of Technology and a law degree from Georgetown University, he had spent years in the private sector. But with previous stints directing tactical warfare programs and acquisition, technology, and logistics at the Pentagon, he was quick to learn. He needed to be. In his first month in office, his troops executed what he called “the largest evacuation of people in U.S. history” in Afghanistan following the Biden administration’s disastrous pullout from the country. In his spare time, he had received plenty of updates on China’s military strength, which, in oblique terms, he shared with the packed conference crowd. His principal focus, as he explained in his address, was China and the threat its rapid military rise posed to the United States and the world at large. His number one concern was China’s increasing capabilities to effectively deploy precision weapons. “For about 20 years,” he said, “I’ve watched the range and target set for these weapons, their sophistication, and their inventories, increase.

“They have now gone from a few hundred miles to thousands to literally around the globe. They have gone from a few high value assets near China’s shores to the second and third island chains, and most recently to intercontinental ranges and even to the potential for global strikes . . . strikes from space even.”
Chinese dominance in space is the newest domain in which the country seeks to overtake the United States and its allies. As military experts underscore, it’s the ultimate high ground… Imagine Pearl Harbor, but a surprise attack not on ships but rather satellites. In such a scenario, American forces would be rendered effectively blind before any amphibious invasion of Taiwan. What you can’t see, you can’t shoot.
Kendall didn’t give any specifics. That sort of information would undoubtedly have been classified. But intelligence sources soon began filling in the details about China’s ability to strike from space. Two months after Kendall assumed command of the U.S. Air Force, PLARF staged a critical test of groundbreaking weapons technology. It launched a Long March rocket carrying a hypersonic glide vehicle (HGV) loaded with a live missile. About five hundred miles above the earth’s surface, the zone scientists call low Earth orbit, where many satellites reside, the HGV was released. Traveling at an estimated seven thousand miles an hour, it circumnavigated most of the globe at altitudes beyond the detection of radar and early warning systems before re-entering the atmosphere.

As the HGV descended near China — part of a flight plan designed to deter monitoring by the West — its outer shell, experts estimate, increased to temperatures between three thousand and five thousand degrees Fahrenheit, the unavoidable result of friction at such super-sonic speeds. Such blistering temperatures pose huge technical and engineering challenges to scientists working on hypersonics, forcing them to search for more stable materials and sleeker designs to ensure both structural and operational stability. The HGV did not melt or explode. It continued at a low trajectory, heading toward its target and releasing its payload.
That first demonstration of a long-range hypersonic bombing expedition wasn’t 100 percent successful — such experimental tests rarely are. American and Asian intelligence sources reported that the missile had landed about twenty-five miles from its intended destination. In a combat situation, that might have been a misfire. To those in scientific, military, and intelligence circles, however, the result was anything but a failure; on the contrary, it was an astonishing achievement. Most importantly, China was learning — and learning quickly. Soon they would master their craft.
Buttressing USAF Secretary Kendall’s remarks in September 2021, one baffled American intelligence source struggled to put these tests into perspective, making the demonstration sound, perhaps, nearly miraculous: “We have no idea how they did this.”
China’s rapid development of this critical emerging technology wasn’t an accident. It was the fruits of a meticulously executed campaign of targeted espionage extensively planned years before. The world’s greatest superpower had stood by as its foremost strategic rival had brazenly stolen one of the technologies behind a critical new weapons system that could wreak havoc on future battlefields.
The precise details of how the PLA built its test hypersonic glide vehicle and fine-tuned what one analyst has termed an orbital glider release system (OGRS) remain largely unknown in the West. (A spokesperson with the Chinese Ministry of Foreign Affairs later denied that the test had happened, insisting that the rocket launch had been conducted merely to verify spacecraft reusability.) But the way the PLA amassed the knowledge and skill to leapfrog over American hypersonic development so quickly should come as no surprise to intelligence insiders.

The CCP’s obsession with obtaining the plans for state-of-the-art Department of Defense initiatives through sophisticated pairings of Human Intelligence (HUMINT) and cyberhacking operations, and pervasive cash-driven talent acquisitions, has been relentless. But a good deal of hypersonic know-how has been cribbed and delivered in plain sight, largely driven by what political scientists and intelligence officers describe as the CCP’s Xi-mandated civil-military fusion: the use of academics, businessmen, and tech professionals to steal technology for the benefit of the country’s military force. The goal in all these operations remains the same: to target critical defense technologies, often developed using billions of dollars of U.S. funds, and steal them to advance China’s military capabilities and erode U.S. and Western air and sea dominance. Chinese dominance in space is the newest domain in which the country seeks to overtake the United States and its allies. As military experts underscore, it’s the ultimate high ground. Establishing domination in this theater could provide China a decisive advantage in the event of any future kinetic conflict with the United States. Imagine Pearl Harbor, but a surprise attack not on ships but rather satellites. In such a scenario, American forces would be rendered effectively blind before any amphibious invasion of Taiwan. What you can’t see, you can’t shoot.
For years, hypersonic missiles, defined as ballistic devices moving up to five and twenty-five times the speed of sound, have transfixed the imaginations of military strategists as a next-generation warfare tool. The tactical advantages are obvious; a delivery system that moves at extremely high speeds and can change course — as opposed to the predictable parabola patterns of most missiles — to hit its targets presents extraordinary deterrence problems for rival armies. How, for example, do you catch up with or intercept a missile that outpaces your own defense capabilities? Meanwhile, the extreme long-range capabilities of hypersonic missiles allows for them to be fired from Earth and then reenter the atmosphere from what has generally been a relatively less monitored military frontier, space.
Understandably concerned about such an extraterrestrial attack scenario, the Department of Defense has invested significantly in hypersonic detection technology. One firm in particular, HRL Laboratories, a Boeing and GE joint venture based in Malibu, California, has been building “space-based missile warning and tracking, space-based surveillance, and airborne infrared countermeasures systems.” Such sensors could be used to detect nuclear missile launches and track both ballistic and hypersonic missiles. In January 2023, HRL hired Chenguang Gong, an electrical engineer, to work as an application-specific integrated circuit (ASIC) manager responsible for tracking the design, development, and performance of readout integrated circuits used in the company’s infrared sensors, a vital component for detecting and tracking missiles and other objects.
The CCP’s obsession with obtaining the plans for state-of-the-art Department of Defense initiatives through sophisticated pairings of Human Intelligence (HUMINT) and cyberhacking operations, and pervasive cash-driven talent acquisitions, has been relentless. But a good deal of hypersonic know-how has been cribbed and delivered in plain sight…
After three months at HRL, Gong, who had been born in China and became a naturalized U.S. citizen in 2011, announced that he was quitting the company, presenting his managers with a rarely heard “It’s not you, it’s me” rationale for doing so. He claimed that “he felt he was not doing a good job and [HRL] should hire someone better,” an FBI agent later testified.
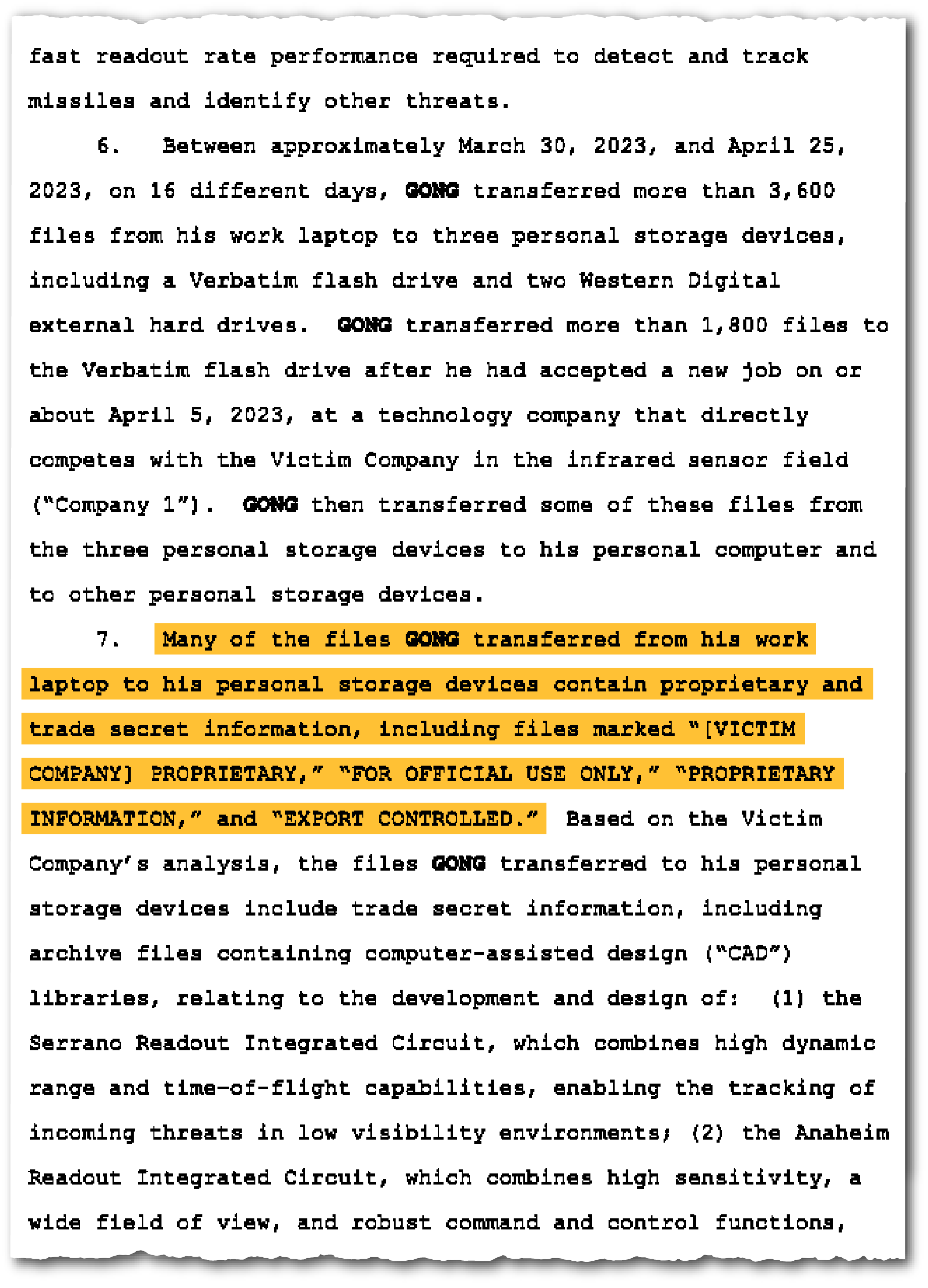
HRL security immediately began evaluating Gong’s computer and network history, eventually discovering that he had downloaded over three thousand company files onto personal storage drives only two weeks before submitting his resignation (the two-week window from when employees leave a firm is often the likeliest time frame for activity by insider threats). The company alerted the FBI, and Special Agent Igor Neyman began investigating. Many of the files were clearly marked as HRL property and designated as “Export Controlled” and “Proprietary Information.” As if that wasn’t clear enough, some files stated even more explicitly that they contained “technical data within the definition of the International Traffic in Arms Regulations and are subject to the export control laws of the U.S. Government.” Other documents bore wording further warning that transmission “by any means to a foreign person, whether in the U.S. or abroad, without an export license or other approval from the U.S. Department of State, is prohibited.”
According to court papers, Chenguang Gong didn’t seem to care much about IP protection at large. His past employment record certainly made that clear. Prior to joining HRL, he had worked with several tech companies, and an FBI forensic analysis of his email communications indicated that he had been stealing documents — many also marked as proprietary — from his previous employers and used such stolen information to apply to several tech companies and CCP-sponsored talent programs from 2013 to 2020. In a proposal sent to the 38th Research Institute of China Electronics Technology Group Corporation, a high-tech research institute in Beijing, for instance, Gong allegedly offered to make high-performance analog-to-digital converters similar to those produced by his American employer. He noted that the global market for those products “is basically monopolized by several companies in the United States” and that the export of those items from the United States requires a “government export license.” In 2019, subsidized by talent program organizers, following a familiar modus operandi of the Chinese intelligence playbook, Gong traveled to China twice to participate in conferences. In 2020, he also reportedly pitched to his prospective Chinese partners manufacturing “low light/night vision” image sensors for use in military night vision goggles and civilian applications and provided clips of a sensor developed by Fairchild Imaging, his employer from 2015 to 2019. Apparently HRL had missed these red flags in their pre-employment background screenings and paid the price for not doing so.
During interviews with the FBI, Gong lied repeatedly about his actions, according to Special Agent Neyman, and frequently changed his story. At that point, he had already accepted a job at HRL’s primary competitor, a career move that made his file copying even more suspect. He started work on May 1, 2024, but ten days later, after learning that Gong had transferred files onto personal storage devices, the new company terminated him. On February 7, 2024, just days before Gong’s planned trip to China, he was indicted for theft of trade secrets.1The Wire China note: Earlier this month Gong pleaded guilty and received a 46-month prison sentence. Meanwhile, according to Neyman, the whereabouts of two of the three storage devices Gong allegedly used to transfer the files on the sensitive schematics for tracking hypersonic missiles, and therefore enabling the means to defend against them by American forces, remain unknown. One can only presume where they most likely ended up.
Excerpted from The Great Heist: China’s Epic Campaign to Steal America’s Secrets by David R. Shedd and Andrew Badger. Copyright 2025 by David R. Shedd and Andrew Badger. Published with permission from Harper Books and HarperCollins Publishers.

David R. Shedd is the former deputy director and acting director of the Defense Intelligence Agency (DIA). He also served as chief of staff for the director of national intelligence and National Security Council senior director and as special assistant to the president for intelligence under George W. Bush. He began his intelligence career in 1982 immediately after his studies at Geneva College and Georgetown University, and served nearly thirty-three years in a wide variety of positions both inside and outside of the CIA during his career.

Andrew Badger is a former DIA case officer and graduate of the CIA’s elite training program, The Farm. He served on the front lines of human intelligence operations, including a 2014 deployment to Afghanistan in support of U.S. military operations. In the private sector, Badger has advised global firms such as McKinsey & Company and Deutsche Bank on geopolitical risk. He holds a bachelor’s degree in government from Harvard and a master’s in diplomatic studies from the University of Oxford, where he is a research associate and lectures on state sponsored espionage.